By Noelyn Nassuuna
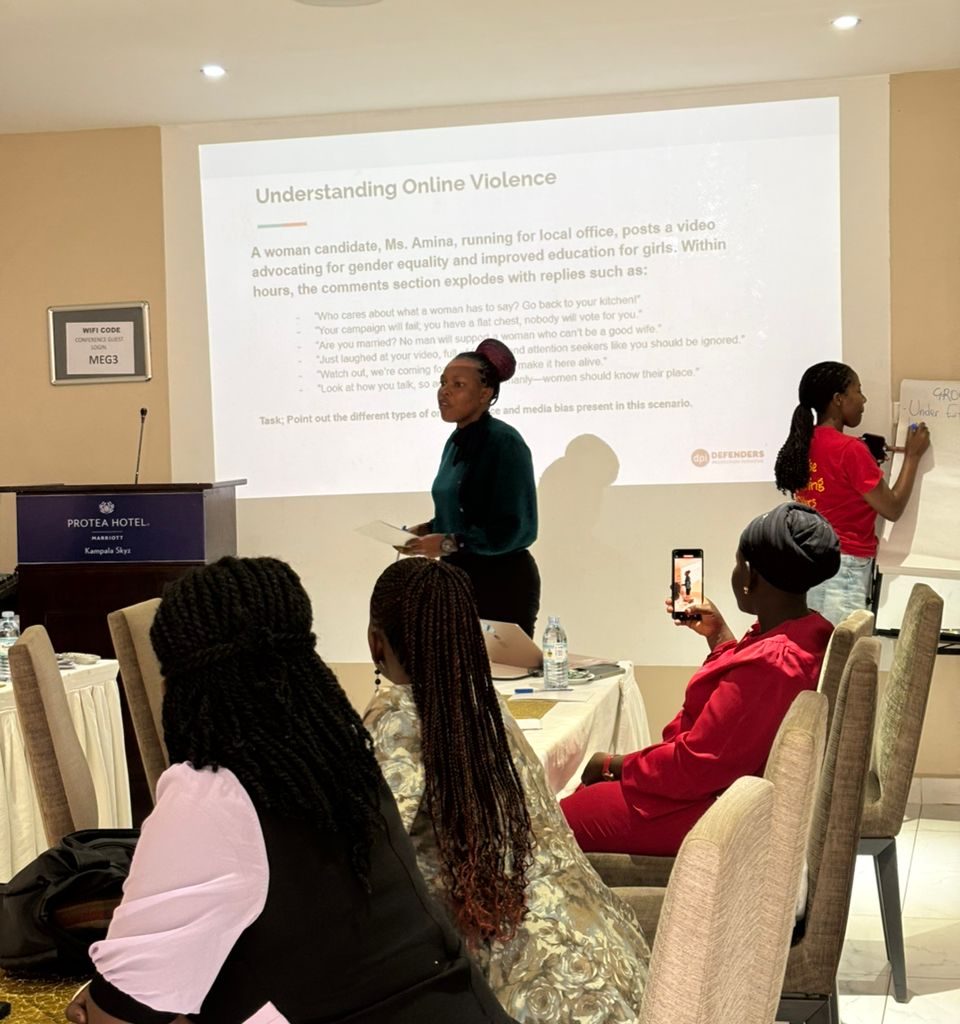
Across social media platforms, caricature portraits and AI-generated avatars have quickly become a popular way for people to express themselves online. From activists and professionals to young girls exploring identity in digital spaces, many users are embracing these stylized images as profile photos or storytelling tools. While the trend looks creative and empowering on the surface, it also raises important questions about digital safety, privacy, and online protection.
A New Layer of Digital Identity
Caricatures allow individuals to present a version of themselves that feels artistic and less exposed than a real photograph. For many women and young users, especially those navigating online harassment or public visibility, avatars can feel safer. They create a sense of distance between personal identity and public presence while still allowing creativity and confidence to shine.
However, digital safety experts caution that caricatures do not always guarantee anonymity. Even stylized images may reflect recognizable features such as hairstyles, skin tone, or cultural symbols. When combined with usernames, captions, or location tags, it becomes easier for someone to connect the avatar back to a real person. This can create a false sense of privacy, where users share more information than they normally would.
The Hidden Risk of Facial Data
Many caricature tools require users to upload several photos to generate their artwork. These images may be processed by artificial intelligence systems, and sometimes stored on external servers. If the platform’s privacy policies are unclear, users may unknowingly give away biometric information such as facial structure or expressions.
For digital rights advocates, this raises concerns about data ownership and consent. Young people and first-time users may not fully understand how their images are used beyond creating a cartoon portrait. Over time, repeated uploads to different apps can expand someone’s digital footprint and increase exposure to data collection practices.
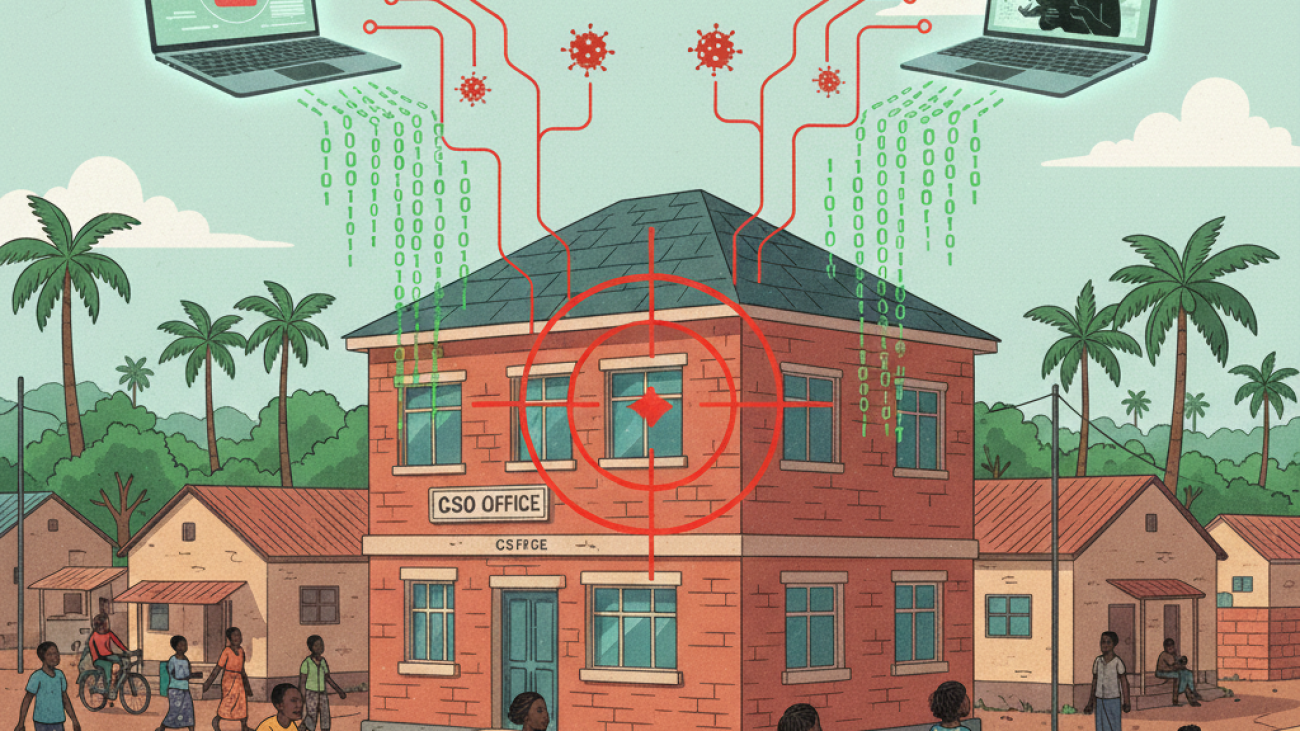
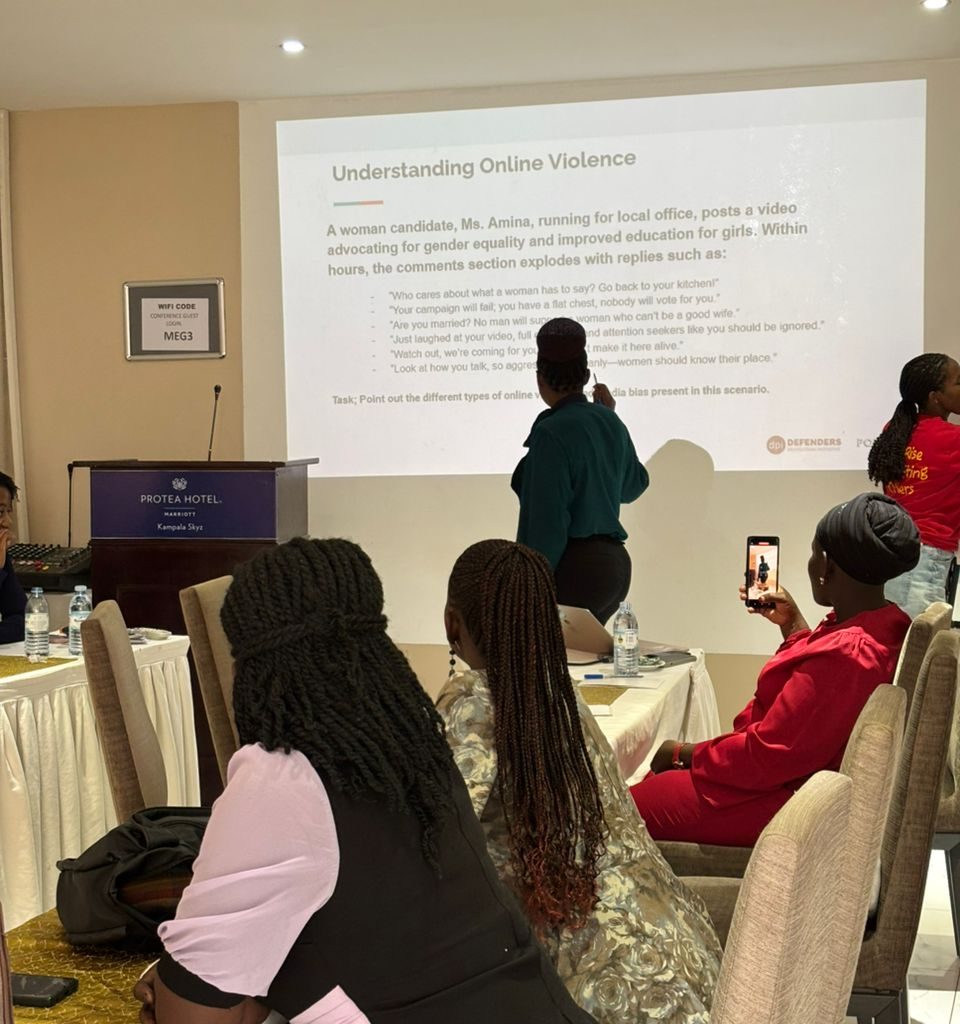
Identity Misuse and Online Harassment
Another growing concern is the potential misuse of caricatures. Screenshots or downloaded avatars can be edited or reposted without permission, which may lead to impersonation or misleading content. In online spaces where women, journalists, or activists already face targeted harassment, even a stylized image can become a tool for unwanted attention.
Digital safety practitioners emphasize the importance of maintaining control over how images are shared. Simple actions such as using trusted platforms, adjusting privacy settings, and avoiding oversharing personal details can reduce risks.
A Positive Opportunity for Protection
Despite these challenges, caricatures can also support safer online engagement when used intentionally. Some advocates choose illustrated avatars instead of real photos to lower direct identification risks. Organizations working with young girls or community leaders have also used caricatures to represent participants without exposing their real faces publicly.
The key difference lies in awareness and informed choice. When users understand the digital implications behind the trend, caricatures can become a creative safety tool rather than a vulnerability.
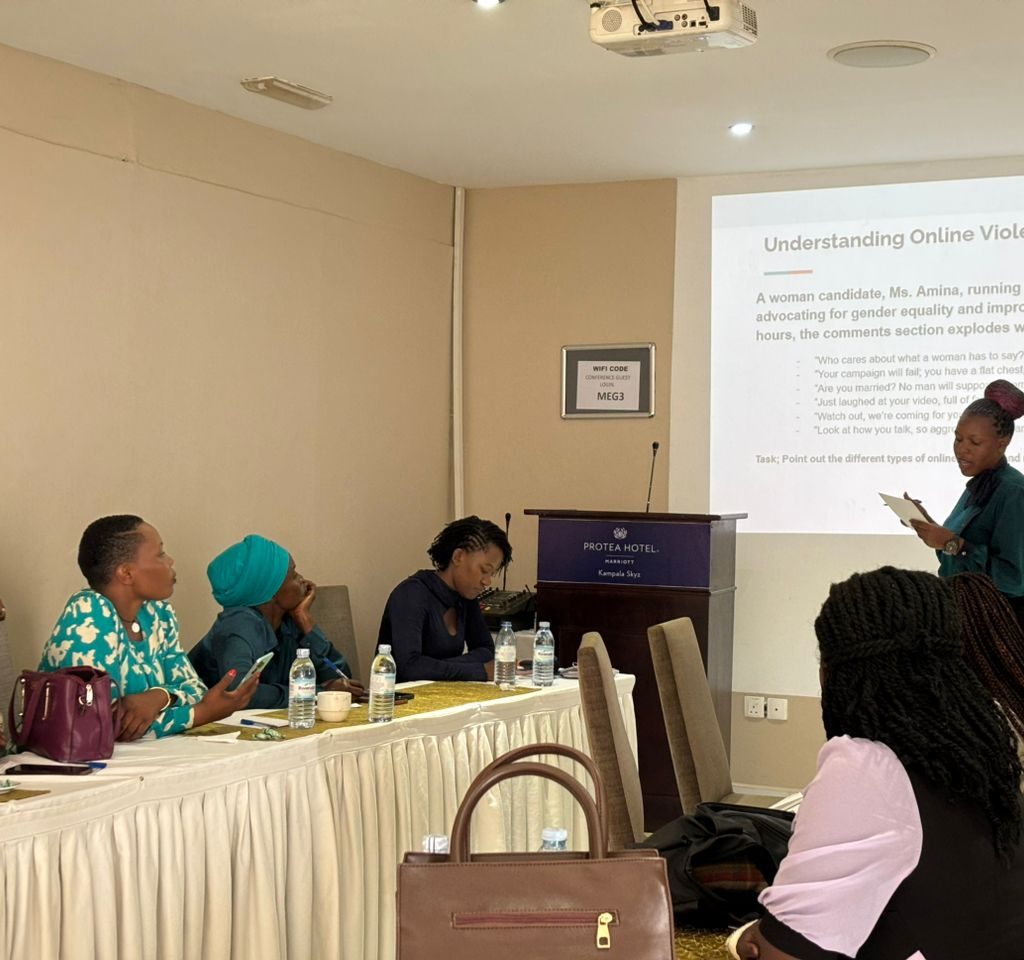
Building a Culture of Digital Awareness
As the caricature trend continues to grow, conversations around digital safety must grow alongside it. Encouraging users to read app permissions, understand data privacy, and think critically about online identity can help create a safer digital environment.
Caricatures are more than just a social media trend, they are part of how people shape identity and community online. By balancing creativity with caution, individuals and organizations can enjoy the benefits of this artistic movement while protecting privacy, dignity, and security in digital spaces.